Table of Contents
Data security is more important than ever. Although business process outsourcing (BPO) is increasingly popular, many fear that partnering with a third-party service provider increases the chance of data and security breaches.
Your whole business is at stake if your data is not kept private and secure. Thus, it is essential to partner with a reliable service provider and understand how they handle data security.
Here are the impacts of a security breach on the BPO industry and the steps reliable BPO vendors take to prevent attacks.
Major Impacts of Security Breach on BPO
To start, what is BPO? It is hiring a third party to perform certain business functions to leverage cost savings and efficiency. Cybersecurity threats or security breaches in BPO involve actions aimed at disrupting, damaging, or stealing sensitive information and exploiting system vulnerabilities.
Cybercriminals, also known as bad actors, use computer viruses and other attack vectors to access the BPO company’s networks. They launch their attack using unsafe or unknown software from a remote location. Alternatively, they may physically breach the site and obtain access to the BPO company’s network from their devices.
A security breach in your BPO provider’s system means potential dangers for your organization and customer data. Here are the consequences of cyberattacks in BPO.
- Financial losses. Security breaches incur significant financial losses. The average data breach cost in 2022 was US$4.35 million, but sources say it could reach $5 million in 2023. Bad actors can steal information that gives them access to financial records and other personal data they can sell.
- Regulatory fines. Failure to prove that the BPO company can safeguard your sensitive data means more cybersecurity threats for your organization. Not meeting minimum regulatory compliance can lead to fines and financial blunders for the BPO provider and client.
- Reputational costs. Service providers must protect client information and deliver excellent customer support. However, privacy issues leading to a massive security breach will inevitably ruin their image and that of their clients. Customers who discover their data is unsafe will likely consider other options and switch to your rivals.
- Operational disruptions. The BPO vendor might take time to recover from massive security breaches, putting their operations and the client’s business functions on hold while they set up the necessary security measures to keep the network protected.
Managing the risk and security of outsourced processes is crucial to ensuring a successful BPO partnership. No company wants privacy and security risks, so third-party vendors and client companies must take active steps to minimize risks.
The easiest way for outsourcing clients to ensure risk-free and safe operations is to partner with a qualified, reputable BPO provider that puts data security at the forefront. In addition, businesses using outsourcing services can take precautions against data breaches by formalizing and enforcing security policies and privacy safeguards.
Ways BPO Companies Handle Data Security
The versatility of outsourcing ensures that businesses of all sizes benefit from reduced costs and higher revenues. It strengthens the market growth of many industries.
The most reliable BPO companies use industry-standard encryption and other safeguards to protect their clients’ data. Reputable vendors will always prioritize BPO security.
Here are the practices that service providers employ to prevent security breaches in their BPO operations:
- Attain ISO certifications. Clients gain insights into the security prowess of the vendor via International Organization for Standardization (ISO) certifications. Qualified BPO companies bear ISO certifications, assuring adherence to regulatory guidelines, standards, and client requisites.
- Implement 24/7 monitoring. Given the potential for security breaches at any hour, BPO companies maintain dedicated information technology (IT) teams available round-the-clock, poised to address emerging issues promptly.
- Engage experienced and trained professionals. Outsourcing vendors exclusively collaborate with proficient IT experts to oversee network security. Seasoned professionals play a pivotal role in minimizing the probability of errors.
- Educate employees on best practices. Esteemed service providers with a history of excellence invest in educating their employees concerning data security best practices. Continuous training and rigorous quality assurance protocols ensure strict policy adherence.
- Adhere to stringent data security policies. BPO companies rigorously uphold stringent data security policies, effectively thwarting threats from infiltrating the network. Authentic data security policies and robust compliance measures safeguard client data.
- Establish comprehensive security measures. Physical security carries equal weight alongside cybersecurity. This encompasses employing specialized locks in restricted areas, authorizing access only for designated personnel, and deploying security cameras. Prominent outsourcing providers diligently adhere to these security protocols.
- Ensure secure communication. BPO companies engage in frequent communication with diverse clients and businesses. Consequently, they vigilantly monitor bandwidth to prevent the sharing or compromise of sensitive information, safeguarding confidential data.
- Employ secure systems and software. The choice of software and systems plays a pivotal role in data security. The availability of cutting-edge multi-layer protection software and hardware significantly influences the security of provider data.
Why Should You Prioritize Data Security When Choosing a BPO Partner
Customers who use outsourcing services entrust the safety of their sensitive information to the provider. These data include intellectual property, financial records, and personal information about staff and end customers.
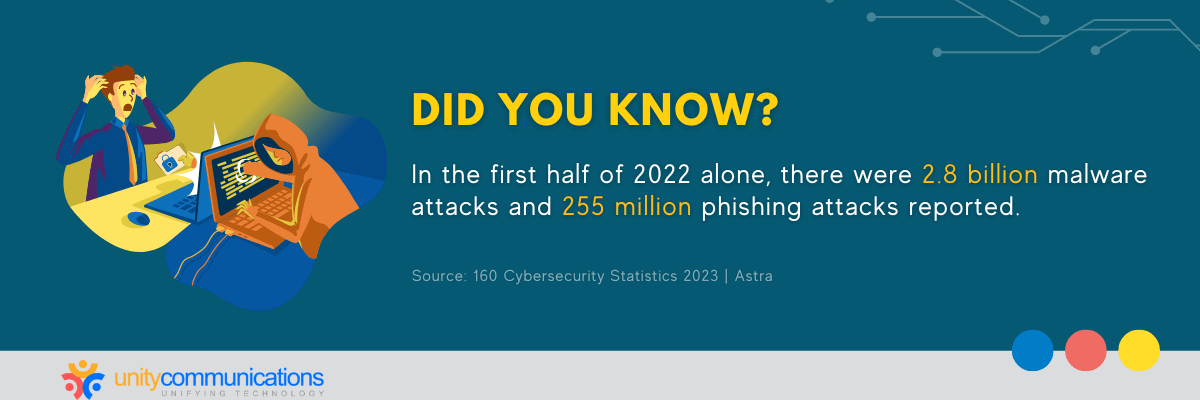
Bad actors are constantly on the hunt to exploit vulnerabilities in data security. The first six months of 2022 alone witnessed 2.8 billion malware attacks and 255 million phishing attacks.
A security breach could lead to legal implications, costly blunders, and reputational damage. Hence, it is important to prioritize data security when choosing a BPO partner.
Moreover, cybersecurity and data privacy are essential to maintaining business continuity. Your BPO partner relies heavily on IT infrastructure, and system disruptions lead to severe consequences. A security breach in the BPO’s network results in system downtime and missed deadlines, which could mean loss of revenue and unhappy end customers for you.
Working with a reputable outsourcing vendor that invests in cybersecurity measures such as intrusion detection, firewalls, and antivirus software helps keep disruptions at bay and ensure business continuity.
The Bottom Line
Outsourcing providers must prioritize cybersecurity due to the industry’s rapid technological advancement. By detecting and addressing cybersecurity risks, they can prevent security breaches in BPO operations. They can also help protect the client’s data, leading to better services and stronger client relationships.
Conversely, outsourcing clients must choose reputable BPO companies that value data privacy and security. By doing so, they can rest assured that their data is safe. With reliable professionals managing their private and sensitive data processes, they leverage security while minimizing costs.
Our experts at Unity Communications provide foolproof BPO solutions and ensure that your information is always safe. Wait no further, and let’s connect!